July 2024 Patch Tuesday: Two Zero-Days and Five Critical Vulnerabilities Amid 142 CVEs
Microsoft has released security updates for 142 vulnerabilities for its July 2024 Patch Tuesday rollout. These include two actively exploited zero-days (CVE-2024-38080 and CVE-2024-38112). Five of the vulnerabilities are rated Critical in severity while the remaining 137 are rated Important or Moderate.
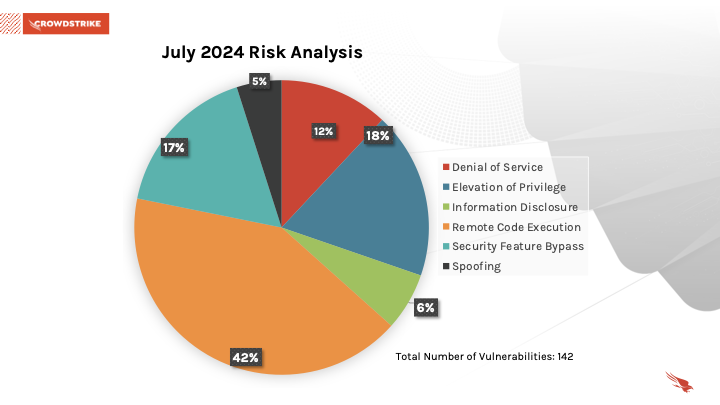
July 2024 Risk Analysis
This month’s leading risk type is remote code execution (42%) followed by elevation of privilege (18%) and security feature bypass (17%).
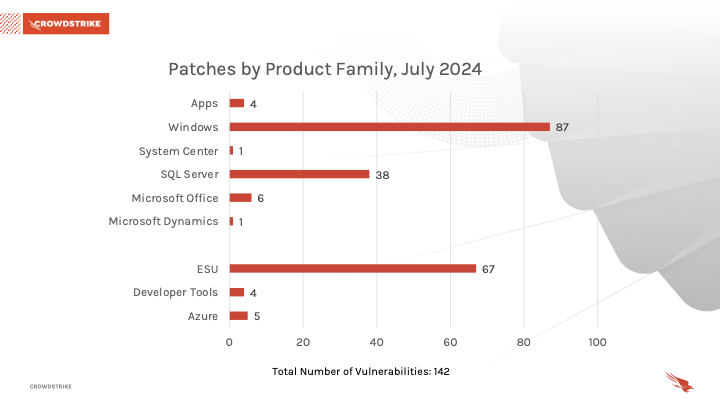
Windows products received the most patches this month with 87, followed by Extended Security Update (ESU) with 67 and SQL Server with 38.
Actively Exploited Zero-Day Vulnerability in Windows Hyper-V
Windows Hyper-V received a patch for CVE-2024-38080, which has a severity of Important and a CVSS score of 7.8. This privilege escalation vulnerability allows an attacker with low-level authentication to elevate access to obtain SYSTEM privileges. Details of the vulnerability, including proof-of-concept for exploiting it, have not been publicly disclosed by Microsoft.
| Severity | CVSS Score | CVE | Description |
| Important | 7.8 | CVE-2024-38080 | Windows Hyper-V Elevation of Privilege Vulnerability |
Table 1. Zero-day in Windows Hyper-V
Actively Exploited Zero-Day Vulnerability Affecting Windows MSHTML Platform
The Windows MSHTML Platform received a patch for CVE-2024-38112, which has a severity of Important and a CVSS score of 7.5. This spoofing vulnerability in the Windows MSHTML Platform, which is used throughout Microsoft 365 and Microsoft Office products, can potentially lead to partial data exposure. The attacker would need to take certain prior actions in order to successfully exploit the vulnerability. Microsoft has not shared details on exactly how the vulnerability is exploited due to its exploitation status. Patching should be done immediately. Please note that MSHTML had another zero-day associated with it earlier this year (CVE-2024-30040).
| Severity | CVSS Score | CVE | Description |
| Important | 7.5 | CVE-2024-38112 | Windows MSHTML Platform Spoofing Vulnerability |
Table 2. Zero-day in Windows MSHTML Platform
Critical Vulnerabilities Affecting Microsoft Windows Remote Desktop Licensing Service, Windows Imaging Component and Microsoft SharePoint Server
CVE-2024-38074, CVE-2024-38076 and CVE-2024-38077 are Critical remote code execution (RCE) vulnerabilities affecting Windows Remote Desktop Licensing Services — and all three have a CVSS score of 9.8. Any of these would allow an unauthenticated attacker to connect to a Remote Desktop Licensing Service and send malicious specially crafted network packets that could allow for remote code execution. Patching should be prioritized even if the service is disabled.
CVE-2024-38060 is a Critical RCE vulnerability affecting Windows Imaging Component and has a CVSS score of 8.8. Successful exploitation of this vulnerability allows for any authenticated attacker to upload a maliciously tagged image file format (TIFF) file to a server, which can lead to remote code execution.
CVE-2024-38023 is a Critical RCE vulnerability affecting Microsoft SharePoint Server and has a CVSS score of 7.2. An authenticated attacker with “Site Owner” permissions or higher from one SharePoint site can use the vulnerability to execute arbitrary code on the SharePoint server, which can affect other sites.
| Severity | CVSS Score | CVE | Description |
| Critical | 9.8 | CVE-2024-38074 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| Critical | 9.8 | CVE-2024-38076 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| Critical | 9.8 | CVE-2024-38077 | Windows Remote Desktop Licensing Service Remote Code Execution Vulnerability |
| Critical | 8.8 | CVE-2024-38060 | Windows Imaging Component Remote Code Execution Vulnerability |
| Critical | 7.2 | CVE-2024-38023 | Microsoft SharePoint Server Remote Code Execution Vulnerability |
Table 3. Critical vulnerabilities in Windows Remote Desktop Licensing, Windows Imaging Component and Microsoft SharePoint Server
Vulnerabilities with Existing Proof-of-Concept Affecting .NET, Visual Studio and ARM-based Operating Systems
CVE-2024-35264 is an Important RCE vulnerability affecting .NET and Visual Studio and has a CVSS score of 8.1. Successful exploitation of this vulnerability requires an attacker to win in a race condition (two or more threads/processes access the same resource) by closing an http/3 stream while the request body is being processed. Microsoft has not shared further details on the vulnerability.
CVE-2024-37985 is an Important information disclosure vulnerability affecting all ARM-based operating systems and has a CVSS score of 5.9. Successful exploitation of this vulnerability allows an attacker to view heap memory (reserved area within memory for data storage) from a privileged process running on the server. An attacker must meet additional conditions prior to exploitation in order to successfully exploit this vulnerability.
| Severity | CVSS Score | CVE | Description |
| Important | 8.1 | CVE-2024-35264 | .NET and Visual Studio Remote Code Execution Vulnerability |
| Important | 5.9 | CVE-2024-37985 | Systematic Identification and Characterization of Proprietary Prefetchers |
Table 4. Vulnerabilities with existing proof-of-concept available in .NET, Visual Studio and ARM-based operating systems
Importance of Prioritizing SQL Server Patching
Thirty-eight of the vulnerabilities this month affect SQL server. Given the importance of SQL servers and the challenges associated with patching these critical servers, we highly recommend prioritizing SQL-related patches given the lead time often necessary for testing and regression.
Not All Relevant Vulnerabilities Have Patches: Consider Mitigation Strategies
As we have learned with other notable vulnerabilities, such as Log4j, not every highly exploitable vulnerability can be easily patched. As is the case for the ProxyNotShell vulnerabilities, it’s critically important to develop a response plan for how to defend your environments when no patching protocol exists.
Regular review of your patching strategy should still be a part of your program, but you should also look more holistically at your organization’s methods for cybersecurity and improve your overall security posture.
The CrowdStrike Falcon® platform regularly collects and analyzes trillions of endpoint events every day from millions of sensors deployed across 176 countries. Watch this demo to see the Falcon platform in action.
Learn More
Learn more about how CrowdStrike Falcon® Exposure Management can help you quickly and easily discover and prioritize vulnerabilities and other types of exposures here.
About CVSS Scores
The Common Vulnerability Scoring System (CVSS) is a free and open industry standard that CrowdStrike and many other cybersecurity organizations use to assess and communicate software vulnerabilities’ severity and characteristics. The CVSS Base Score ranges from 0.0 to 10.0, and the National Vulnerability Database (NVD) adds a severity rating for CVSS scores. Learn more about vulnerability scoring in this article.
Additional Resources
- For more information on which products are in Microsoft’s Extended Security Updates program, refer to the vendor guidance here.
- Read the CrowdStrike 2024 Global Threat Report to learn how the threat landscape has shifted and understand the adversary behavior driving these shifts.
- See how Falcon Exposure Management can help you discover and manage vulnerabilities and other exposures in your environments.
- Learn how CrowdStrike’s external attack surface module, CrowdStrike® Falcon Surface™, can discover unknown, exposed and vulnerable internet-facing assets, enabling security teams to stop adversaries in their tracks.
- Make prioritization painless and efficient. Watch how CrowdStrike Falcon® Spotlight enables IT staff to improve visibility with custom filters and team dashboards.
- Test CrowdStrike next-gen antivirus for yourself with a free trial of CrowdStrike® Falcon Prevent™.