Identity is at the center of the fight against adversaries. As threat actors weaponize legitimate credentials and sell access to the highest bidders, organizations must proactively detect and secure exposed identities to shut down potential attack paths before they can be exploited.
The CrowdStrike 2025 Global Threat Report illustrates the urgent need for strong identity protection as adversaries explore new techniques. Social engineering is growing in popularity: Voice phishing (vishing) attacks surged by 442% between the first and second half of 2024 as groups like CURLY SPIDER trick employees into handing over login details. Those who don’t steal credentials can buy them — access broker activity was up nearly 50% in 2024, reflecting the growing market for illicit access. Further, more than half (52%) of observed vulnerabilities in 2024 were tied to initial access.
With their credentials in the crosshairs, organizations need a faster, smarter approach to detect and stop adversary activity in real time. CrowdStrike Falcon® Identity Protection delivers this speed and intelligence by harnessing the power of the CrowdStrike Falcon® platform and its world-class threat intelligence and unifying identity protection across hybrid environments. Falcon Identity Protection helps organizations detect and stop identity-based threats before they escalate — even when they use legitimate credentials.
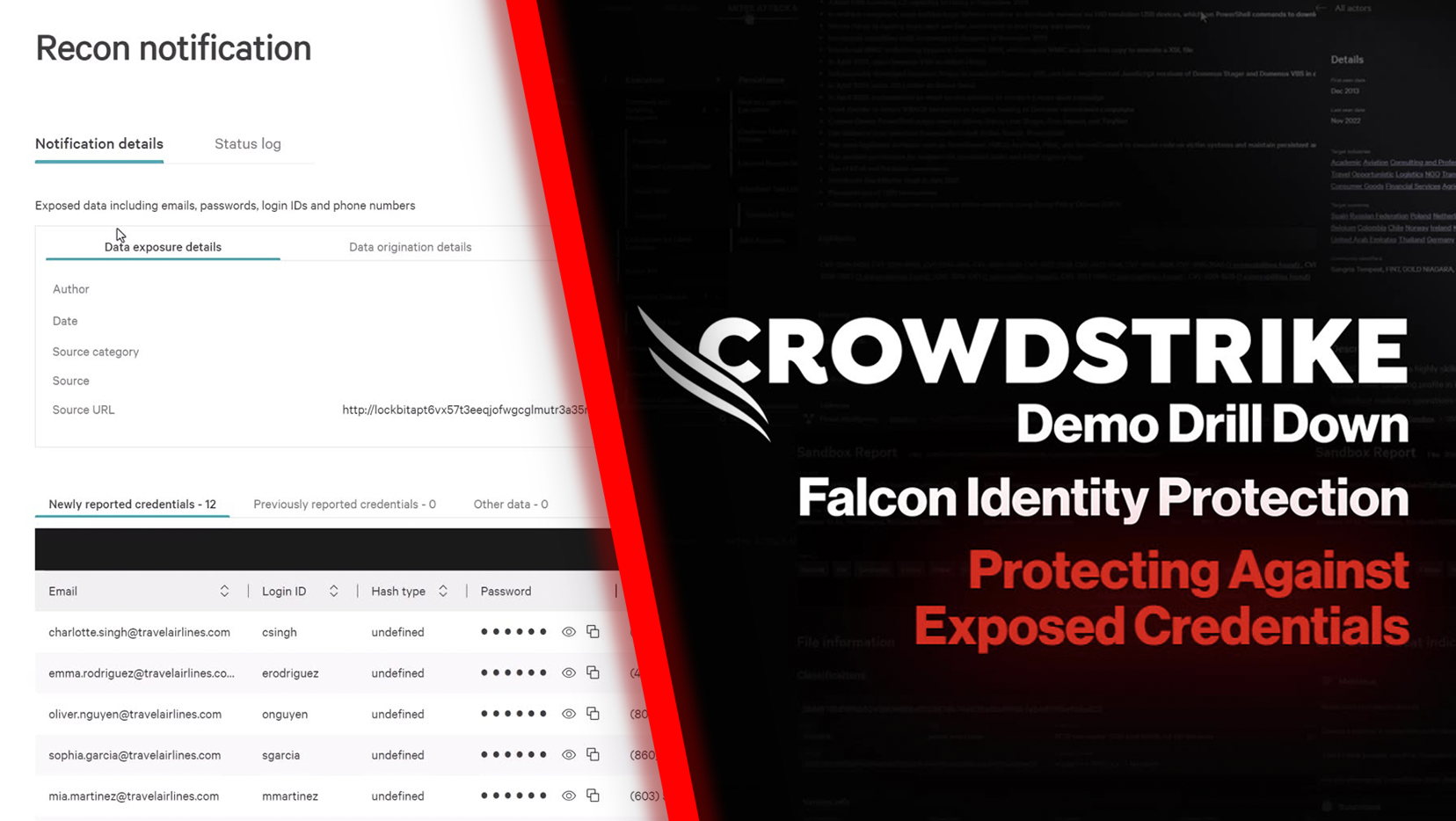
Detect and Respond to Exposed Credentials
Organizations can stay ahead of this growing threat by leveraging Falcon Identity Protection along with the Recon function in CrowdStrike Falcon® Adversary Intelligence, which seamlessly integrate to detect and mitigate exposed credentials in real time.
The following scenario demonstrates how with this integration, Falcon Identity Protection responds to credentials exposed by access brokers. A Recon notification reveals a data exposure involving the fictitious company: Awesome Health Network. The activity is linked to LockBit, a notorious ransomware-as-a-service operation. Further investigation shows that BITWISE SPIDER — a well-known eCrime adversary with a history of leveraging LockBit — has ties to this exposure event, underscoring the urgent need for swift action.




![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1)