Featured Articles
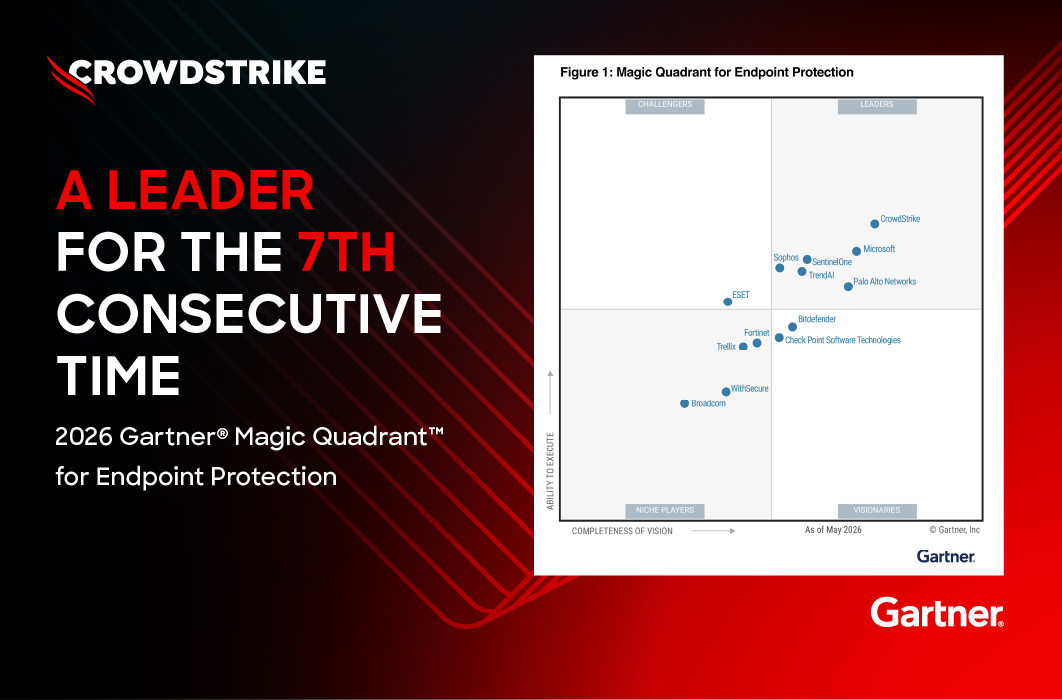
CrowdStrike Named a Leader in 2026 Gartner® Magic Quadrant™ for Endpoint Protection for Seventh Consecutive Time
CrowdStrike has once again been named a Leader in the 2026 Gartner® Magic Quadrant™ for Endpoint Protection. This marks the seventh consecutive time we have received this recognition, and for the four[…]
CrowdStrike Named a Leader in Identity Threat Detection and Response
Two recent industry reports validate CrowdStrike’s leadership in the identity threat detection and response (ITDR) market: Frost & Sullivan has named CrowdStrike its 2026 Company of the Year for Ident[…]
Disrupting Glassworm: Inside CrowdStrike’s Takedown of a Developer-Targeting Botnet
On May 26, 2026, at 14:00 UTC, the CrowdStrike Counter Adversary Operations team executed a coordinated takedown of the Glassworm botnet, a global threat targeting software developers through the open[…]
New Claude Integration Brings Audit Data into the Falcon Platform
As organizations scale Anthropic’s Claude model across their workforce, they need the same level of auditability around AI platform activity that they expect from every other enterprise application. A[…]
Now Live: The CrowdStrike 2026 Financial Services Threat Landscape Report
The financial services industry is the fourth most-targeted sector globally, accounting for 12% of all observed activity. eCrime and nation-state adversaries spanning all motivations target these orga[…]
Falcon AIDR Detects Threats at the Prompt Layer in Kubernetes AI Applications
AI is introducing a new class of threats that don’t look like traditional attacks and can’t be detected with conventional tools. The AI applications that organizations deploy in the cloud interact wit[…]
CrowdStrike Named a Leader in the First-Ever Gartner® Magic Quadrant™ for Cyberthreat Intelligence Technologies
CrowdStrike has been named a Leader in the inaugural 2026 Gartner® Magic Quadrant™ for Cyberthreat Intelligence Technologies and positioned furthest to the right in Completeness of Vision among all ve[…]
CrowdStrike Launches Falcon OverWatch for Defender
CrowdStrike is excited to announce Falcon OverWatch for Defender, a new offering that extends our elite managed threat hunting to Microsoft Defender environments. The need for proactive threat hunting[…]
Defending Against CORDIAL SPIDER and SNARKY SPIDER with Falcon Shield
Since October 2025, CrowdStrike Counter Adversary Operations has observed a shift in intrusion tradecraft: Threat actors are executing high-speed, SaaS-centric attacks that bypass traditional endpoint[…]
CrowdStrike Expands Real-Time Cloud Detection and Response to Google Cloud
Complexity has become a defining security challenge as organizations expand across hybrid and multi-cloud environments. In fact, 52% of surveyed organizations ranked multi/hybrid cloud complexity amon[…]






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)

?wid=2048&hei=1350&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)