Microsoft has released security updates for 150 vulnerabilities in its April 2024 Patch Tuesday rollout, a much larger amount than in recent months. There are three Critical remote code execution vulnerabilities (CVE-2024-21322, CVE-2024-21323 and CVE-2024-29053), all of which are related to Microsoft Defender for IoT, Microsoft’s security platform for IoT devices.
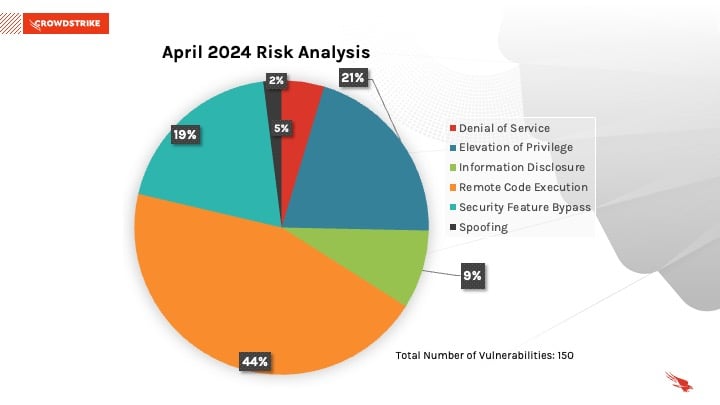
April 2024 Risk Analysis
This month’s leading risk type is remote code execution (RCE), accounting for 44%, followed by elevation of privilege (21%) and security feature bypass (19%).
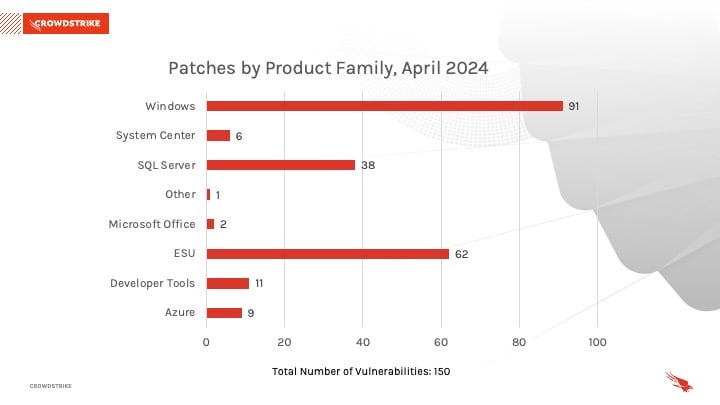
Windows products received the most patches this month with 91, followed by Extended Security Update (ESU) with 62 and SQL Server with 38. This represents a consistent uptick in vulnerabilities identified in Extended Support products. In order to ensure the security of endpoints, upgrade to a supported version or purchase Extended Support from the vendor.
Critical Remote Code Execution Vulnerabilities Affect Microsoft Defender for IoT
CVE-2024-21323 is a Critical RCE vulnerability affecting Microsoft Defender for IoT and has a CVSS score of 8.8. Successful exploitation of this vulnerability would allow an attacker to send malicious update files to the Defender for IoT sensor, allowing the attacker to overwrite any file on the managed asset. This vulnerability requires the attacker to be authenticated into the IoT sensor with just enough permissions to begin the update process. Any IoT device with the Defender sensor deployed should be updated as soon as possible.
CVE-2024-29053 is another Critical RCE vulnerability that affects the Microsoft Defender for IoT platform and has a CVSS score of 8.8. Successful exploitation of this vulnerability could allow an unauthenticated attacker to upload malicious files to sensitive locations on the server appliance. Leveraging this vulnerability, the attacker could override any files including sensitive ones, thereby disrupting normal operation or inhibiting visibility into the IoT network.
CVE-2024-21322 is yet another Critical RCE vulnerability affecting Microsoft Defender for IoT and has a CVSS score of 7.2. Successful exploitation of this vulnerability would allow the attacker to send arbitrary commands to the managed device, possibly impeding normal functioning of the Defender for IoT monitoring software. This vulnerability requires the attacker to be an administrator of the management console of Defender for IoT on the web. Regular audits and validation of such accounts should be performed to limit risk.
| Severity | CVSS Score | CVE | Description |
| Critical | 8.8 | CVE-2024-21323 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| Critical | 8.8 | CVE-2024-29053 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
| Critical | 7.2 | CVE-2024-21322 | Microsoft Defender for IoT Remote Code Execution Vulnerability |
Table 1. Critical vulnerabilities in Microsoft Defender for IoT
Not All Relevant Vulnerabilities Have Patches: Consider Mitigation Strategies
As we have learned with other notable vulnerabilities, such as Log4j, not every highly exploitable vulnerability can be easily patched. As is the case for the ProxyNotShell vulnerabilities, it’s critically important to develop a response plan for how to defend your environments when no patching protocol exists.
Regular review of your patching strategy should still be a part of your program, but you should also look more holistically at your organization's methods for cybersecurity to improve your overall security posture.
The CrowdStrike Falcon® platform regularly collects and analyzes trillions of endpoint events every day from millions of sensors deployed across 176 countries. Watch this demo to see the Falcon platform in action.
Learn More
Learn more about how CrowdStrike Falcon® Exposure Management can help you quickly and easily discover and prioritize vulnerabilities and other types of exposures here.
About CVSS Scores
The Common Vulnerability Scoring System (CVSS) is a free and open industry standard that CrowdStrike and many other cybersecurity organizations use to assess and communicate software vulnerabilities’ severity and characteristics. The CVSS Base Score ranges from 0.0 to 10.0, and the National Vulnerability Database (NVD) adds a severity rating for CVSS scores. Learn more about vulnerability scoring in this article.
Additional Resources
- For more information on which products are in Microsoft’s Extended Security Updates program, refer to the vendor guidance here.
- Read the CrowdStrike 2024 Global Threat Report to learn how the threat landscape has shifted in the past year and understand the adversary behavior driving these shifts.
- See how Falcon Exposure Management can help you discover and manage vulnerabilities and other exposures in your environments.
- Learn how CrowdStrike’s external attack surface module, CrowdStrike® Falcon Surface™, can discover unknown, exposed and vulnerable internet-facing assets, enabling security teams to stop adversaries in their tracks.
- Learn how CrowdStrike Falcon® Identity Protection products can stop workforce identity threats faster.
- Make prioritization painless and efficient. Watch how CrowdStrike Falcon® Spotlight enables IT staff to improve visibility with custom filters and team dashboards.
- Test CrowdStrike next-gen antivirus for yourself with a free trial of CrowdStrike® Falcon Prevent™.






![Helping Non-Security Stakeholders Understand ATT&CK in 10 Minutes or Less [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/video-ATTCK2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)
![Qatar’s Commercial Bank Chooses CrowdStrike Falcon®: A Partnership Based on Trust [VIDEO]](https://assets.crowdstrike.com/is/image/crowdstrikeinc/Edward-Gonam-Qatar-Blog2-1?wid=530&hei=349&fmt=png-alpha&qlt=95,0&resMode=sharp2&op_usm=3.0,0.3,2,0)